What is the Sidecar Pattern?
The sidecar pattern deploys a secondary process alongside the main application in the same host or Kubernetes pod. The sidecar and the main application share the same network namespace, communicating over local loopback rather than over a network. This eliminates network overhead for calls between them and gives the application low-latency access to sidecar capabilities.
In software architecture, sidecars appear across many contexts: service meshes use sidecars (Envoy, Linkerd) to intercept and manage network traffic; observability platforms use sidecars to collect logs and metrics; data runtimes use sidecars to serve accelerated data and run local inference. The underlying concept is the same in each case: co-locate a helper process with the application it serves to reduce communication overhead and decouple concerns.
The pattern takes its name from motorcycle sidecars -- an additional compartment attached to the side of the main vehicle. The sidecar depends on the motorcycle to operate but handles its own responsibilities.
How the Sidecar Pattern Works
In a Kubernetes deployment, the sidecar runs as a second container within the same Pod as the main application. Because containers in a Kubernetes Pod share the same network namespace, they communicate over localhost -- the loopback interface. There is no DNS resolution, no load balancer, and no network hop.
Key properties of sidecar deployments:
- Loopback communication. Calls from the application to the sidecar travel over the loopback interface. Round-trip latency is measured in microseconds, not milliseconds.
- Shared lifecycle. In Kubernetes, all containers in a Pod start and stop together. The sidecar's lifecycle is coupled to the application's. When the application pod restarts, the sidecar restarts too.
- Independent process. Despite sharing a Pod, the sidecar runs as a separate process with its own CPU, memory, and filesystem. It does not share memory address space with the application (unlike a library).
- Per-instance deployment. Each application pod gets its own dedicated sidecar instance. There is no sharing between pods -- each sidecar is isolated to its co-located application.
On non-Kubernetes infrastructure (bare metal, VMs, Docker Compose), the sidecar runs as a separate process on the same host, connected to the application over 127.0.0.1.
The Sidecar Pattern vs. Background Services
In classic multi-process application design, "background service" and "sidecar" are similar concepts. The key distinctions in modern distributed systems:
Sidecar specifically implies co-location with a single application instance -- one sidecar per application pod. It is not shared across applications. Its purpose is to extend the capabilities of that specific application instance.
Background service (microservice) runs independently and is shared across multiple callers. It scales independently, has its own deployment lifecycle, and is accessed over the network.
The sidecar is a private extension of the application. The microservice is a shared infrastructure component. For a full comparison of these patterns in the context of data runtimes, see Sidecar vs Microservice Architecture.
When the Sidecar Pattern Makes Sense
Latency-critical data access
When an application needs to query data in the hot path of a request -- for real-time fraud scoring, inline personalization, or sub-millisecond cache lookups -- a network round-trip to a remote service adds latency that is hard to eliminate. A sidecar serving locally cached data over loopback can respond in under a millisecond, indistinguishable from an in-process call with the operational simplicity of a separate process.
Local AI inference
Running an LLM or embedding model inference alongside the application means embeddings and completions do not leave the host. The sidecar handles model loading, threading, and batching while the application calls it over a simple HTTP or gRPC API on localhost. This pattern is increasingly common for privacy-sensitive workloads where inference must remain inside a trust boundary.
Service mesh data planes
Envoy Proxy, the sidecar component in Istio and other service meshes, intercepts all inbound and outbound network traffic from the application. Because it runs as a sidecar, it can apply mTLS, circuit breaking, retries, and observability instrumentation without modifying the application code. The sidecar handles cross-cutting concerns; the application focuses on business logic.
Log and metrics agents
Observability agents (Fluent Bit, the OpenTelemetry Collector, Datadog Agent) run as sidecars to collect logs, traces, and metrics from the co-located application. The application writes to a local socket or shared volume; the agent batches and forwards to the observability backend. This decouples telemetry collection from the application's primary process.
Edge and offline resilience
When applications run at edge locations with unreliable connectivity, a sidecar caching critical data locally ensures the application continues serving requests during network outages. The sidecar loads data from a central cluster when connected and serves from its local cache when disconnected. This availability pattern is not possible with a remote service dependency.
Sidecar Resource Considerations
Every sidecar consumes CPU and memory on the application pod's node. The resources are not shared with other pods -- each sidecar is dedicated to its pod.
Memory: A sidecar used for local data acceleration needs enough memory to hold its working dataset. A sidecar caching 500 MB of data with an Arrow in-memory engine needs approximately 500 MB of container memory plus overhead for query execution. This must be reserved in the pod spec.
CPU: Data serving sidecars are typically CPU-light during steady-state query serving (especially for in-memory columnar data). CPU usage peaks during data refresh cycles -- when the sidecar pulls updated data from an upstream source or cluster.
Aggregate cluster cost: With many application pods, the total resource cost of sidecar duplication becomes significant. 50 pods each with a sidecar using 1 GB RAM means 50 GB of RAM allocated across the cluster for sidecars alone. This overhead is the primary argument for centralizing to a microservice at large scale.
Sidecar Pattern in Data and AI Platforms
Data and AI runtimes have adopted the sidecar pattern because it addresses the latency requirements of latency-sensitive application-serving workloads that remote shared services cannot meet.
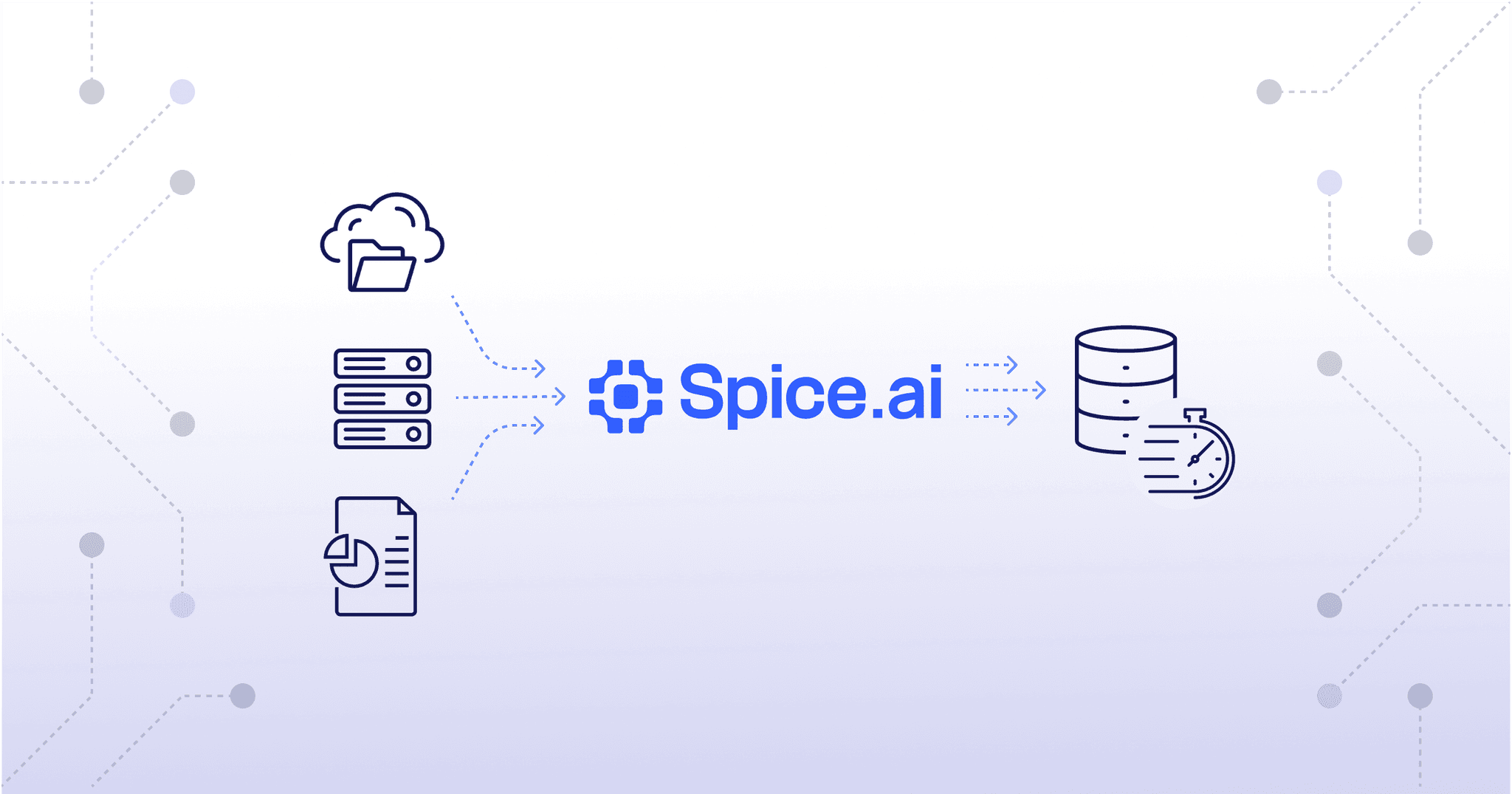
A data runtime sidecar typically:
- Connects to one or more upstream data sources (databases, object stores, warehouses) at startup
- Loads a configured working set of data locally using acceleration
- Keeps that data synchronized using CDC-based incremental refresh or scheduled full refresh
- Serves SQL queries from the application over a local endpoint (Arrow Flight SQL, HTTP, gRPC)
From the application's perspective, the sidecar is a local database. Queries execute against in-memory or on-disk accelerated data with sub-millisecond latency. The application code does not need to know whether the sidecar is serving from a local cache or delegating to an upstream source -- the SQL interface is identical either way.
In a hybrid data architecture, sidecars serve the hot path while a centralized cluster handles data ingestion, refresh pipelines, and large analytical queries. Sidecars transparently delegate cache-miss queries to the cluster over Arrow Flight gRPC, with the application unaware of which tier served each request.
Sidecar Pattern in Service Meshes
Service mesh sidecars are the most widely deployed example of the sidecar pattern at scale. Envoy Proxy (used in Istio, Consul Connect, and others) runs as a sidecar in every application pod and intercepts all network traffic:
- Inbound traffic passes through the sidecar proxy before reaching the application
- Outbound traffic passes through the sidecar before leaving the pod
This interception allows the service mesh to apply consistent policies (mTLS, rate limiting, circuit breaking, retries) and collect consistent telemetry (request counts, latency percentiles, error rates) across all services without any application changes.
The sidecar proxy is opaque to the application -- from the application's perspective, it sends requests to service-name:port and receives responses. The sidecar handles the TLS termination, retries, and observability transparently.
Advanced Topics
Init Containers and Startup Ordering
In Kubernetes, init containers run to completion before the main application containers start. In some sidecar deployments, an init container pre-populates a shared volume or performs startup bootstrapping (e.g., loading an initial dataset snapshot) before the main application and sidecar containers start.
As of Kubernetes 1.29, sidecar containers can be declared with restartPolicy: Always in the init container list, giving Kubernetes native sidecar semantics: the sidecar starts before the application, restarts on failure without terminating the pod, and is guaranteed to terminate after the application container. This addresses a historical challenge where sidecar containers had no lifecycle guarantees relative to the application.
Memory-Mapped Storage in Sidecars
For sidecars serving large local datasets, memory-mapped files offer a significant advantage over loading data fully into heap memory. Memory-mapped files are backed by the operating system's page cache. Pages are loaded on demand (on first access) and evicted by the OS when memory pressure increases. The RSS (Resident Set Size) of the sidecar grows only as accessed pages are loaded, rather than immediately consuming memory for the full dataset.
The Vortex columnar format used in Spice Cayenne is designed for memory-mapped access. Encoded data is read directly from the mapped file without decompression into a separate buffer, which reduces memory usage and improves scan throughput for large cached datasets.
Container Resource Limits and QoS Class
Kubernetes assigns a Quality of Service (QoS) class to each pod based on its resource requests and limits. Pods with both CPU and memory requests equal to limits are assigned the Guaranteed QoS class, which makes them the last to be evicted under node memory pressure. For latency-critical sidecar deployments, setting matching requests and limits ensures the pod is not evicted during resource contention.
Sidecar containers within a pod share the pod's QoS class. If the application container has Guaranteed QoS, the sidecar also receives Guaranteed QoS, protecting both from eviction.
Sidecar Deployment with Spice
Spice is designed to run in sidecar mode alongside applications in Kubernetes. The Spice runtime deploys as a container within the application pod, connects to configured data sources, loads the declared datasets into a local acceleration engine (Arrow in-memory, DuckDB on-disk, or Vortex via Spice Cayenne), and exposes them through Arrow Flight SQL, HTTP, and gRPC on localhost.
In a typical Kubernetes deployment:
# kubernetes/deployment.yaml (abbreviated)
spec:
containers:
- name: app
image: myapp:latest
env:
- name: SPICE_ENDPOINT
value: "localhost:50051" # Arrow Flight SQL on loopback
- name: spice
image: spiceai/spiceai:latest
volumeMounts:
- name: spicepod-config
mountPath: /appThe application queries Spice over localhost:50051 (Arrow Flight SQL) or localhost:8090 (HTTP). All query planning, federation, and local acceleration happen within the sidecar -- the application sends SQL and receives results with sub-millisecond latency for accelerated datasets.
When the sidecar receives a query for data not in its local cache, it transparently delegates to the centralized Spice cluster or queries the upstream source directly. The application sees identical SQL semantics regardless of which path the query takes. For a full comparison of sidecar and microservice deployment modes, see Sidecar vs Microservice Architecture.
Sidecar Pattern FAQ
What is the sidecar pattern?
The sidecar pattern deploys a secondary process alongside the main application in the same host or Kubernetes pod. The sidecar and application share the same network namespace and communicate over local loopback, eliminating network overhead. The sidecar handles specific responsibilities (data caching, network proxying, observability) while the application focuses on business logic.
How does the sidecar pattern differ from a microservice?
A sidecar is co-located with a single application instance and is private to that instance. A microservice runs as an independent, shared service accessed over the network by multiple callers. Sidecars provide lower latency (loopback vs. network) but consume resources per-instance. Microservices share resources across callers but add network latency. See the full comparison at Sidecar vs Microservice Architecture.
What are the resource implications of the sidecar pattern?
Each sidecar consumes dedicated CPU and memory on its pod's node. With many application replicas, the total cluster cost of sidecar duplication multiplies. A sidecar using 1 GB of RAM in a 50-pod deployment consumes 50 GB of RAM across the cluster. For large-scale deployments where resource efficiency matters more than absolute latency, a centralized microservice may be more cost-effective.
How is the sidecar pattern used in service meshes?
Service meshes like Istio deploy Envoy Proxy as a sidecar in each application pod. The proxy intercepts all inbound and outbound traffic, applying mTLS, circuit breaking, retries, and telemetry collection without any application changes. Because Envoy runs as a sidecar, it shares the pod network namespace and can intercept all traffic at the loopback level.
Can sidecars be used for local AI inference?
Yes. Running an LLM or embedding model as a sidecar keeps inference on the same host as the application, eliminating network latency for inference calls and avoiding data leaving the trust boundary. The application calls the sidecar over localhost with a standard API (OpenAI-compatible HTTP, gRPC). This pattern is common for privacy-sensitive workloads and latency-critical AI applications.
Learn more about sidecar deployment
Documentation and guides on deploying Spice as a sidecar for sub-millisecond data access.
Deployment Architecture Docs
Learn how to deploy Spice as a sidecar alongside your application for sub-millisecond data access and local AI inference.
A Developer's Guide to Understanding Spice AI
An explanation of how Spice deploys as a sidecar data and AI runtime alongside applications.
Getting Started with Spice.ai SQL Query Federation & Acceleration
Learn how to use Spice to federate and accelerate queries in sidecar mode.
See Spice in action
Get a guided walkthrough of how development teams use Spice to query, accelerate, and integrate AI for mission-critical workloads.
Get a demo